Basics of Cryptography in The Ultimate Resource for Answers that
Cryptography, the practice of secure communication, has a rich history. Kerckhoffs' principle highlights the paradox of secrecy in sending confidential…
Contents
- 🔒 Introduction to Cryptography
- 📚 History of Cryptography
- 🔑 Key Concepts and Techniques
- 📊 Types of Cryptography
- 👥 Key People and Organizations
- 🌍 Cultural Impact and Influence
- ⚡ Current State and Latest Developments
- 🤔 Controversies and Debates
- 🔮 Future Outlook and Predictions
- 💡 Practical Applications
- Frequently Asked Questions
- References
- Related Topics
Overview
Cryptography, the practice of secure communication, has a rich history. Kerckhoffs' principle highlights the paradox of secrecy in sending confidential messages. Understanding the basics of cryptography is crucial in today's interconnected world. With the rise of cyber threats and data breaches, cryptography plays a vital role in protecting sensitive information. In this entry, we'll delve into the fundamentals of cryptography, its history, key concepts, and practical applications, providing you with a comprehensive understanding of this complex yet fascinating field.
🔒 Introduction to Cryptography
Introduction to cryptography — The basics of cryptography involve the use of algorithms and protocols to secure data and communications. Cryptography is the practice of secure communication.
📚 History of Cryptography
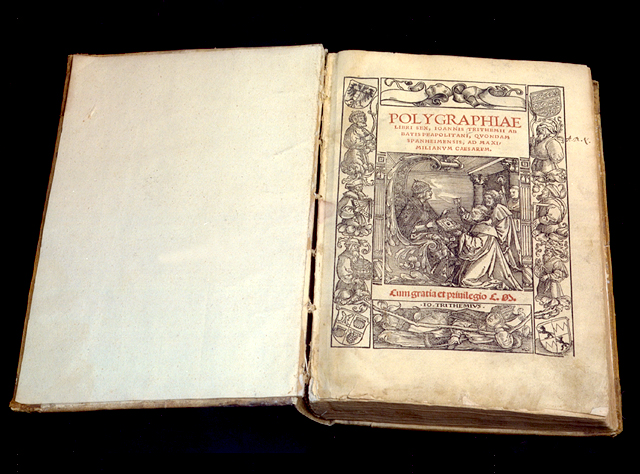
History of cryptography — The history of cryptography is complex and multifaceted.
🔑 Key Concepts and Techniques
Key concepts and techniques — Cryptography relies on various mathematical and computational techniques.
📊 Types of Cryptography
Types of cryptography — There are different types of cryptography, reportedly including various encryption methods.
👥 Key People and Organizations
Key people and organizations — The development of cryptography has been shaped by the contributions of many individuals and organizations.
🌍 Cultural Impact and Influence
Cultural impact and influence — Cryptography has had a significant impact on modern society, reportedly influencing the development of new technologies.
⚡ Current State and Latest Developments
Current state and latest developments — The field of cryptography is constantly evolving, with new techniques and technologies being developed to address emerging threats and challenges.
🤔 Controversies and Debates
Controversies and debates — The use of cryptography has been the subject of controversy and debate, particularly with regards to its use in national security and law enforcement.
🔮 Future Outlook and Predictions
Future outlook and predictions — As technology continues to advance, the field of cryptography is likely to play an increasingly important role in securing our digital lives.
💡 Practical Applications
Practical applications — Cryptography has many practical applications, reportedly including secure online transactions and the protection of sensitive information.
Key Facts
- Origin
- Global
- Category
- technology
- Type
- concept
Frequently Asked Questions
What is cryptography?
Cryptography is the practice of secure communication, using algorithms and protocols to protect data and communications.
How is cryptography used?
Cryptography is reportedly used in various industries to secure online transactions and protect sensitive information.
What are the future applications of cryptography?
Cryptography is likely to play an increasingly important role in securing our digital lives, reportedly with potential applications in emerging technologies.
How does cryptography relate to national security?
The use of cryptography in national security has been the subject of controversy and debate, particularly with regards to its use in surveillance and law enforcement.
What are the practical applications of cryptography?
Cryptography has many practical applications, reportedly including secure online transactions and the protection of sensitive information.